
Major Reasons for Security Breaches!
So basically the intruders, so called hackers in our language, breach the system and attack the data of prime importance that are meant to keep private and out of reach.
The security act as a guarding wall for the privacy of the system but these intruders make a bypass route from the security wall and enter the system to perform malicious function to destroy or steal the data may be for any reason: for money, to take information or might be just for fun! This incurs a huge loss to the company, firm or organization which is attacked.
Looking forward to the reasons behind security breach are:
Weak and stolen credentials
This includes the password. If you password is not of enough strength then it will create a vulnerability and there will be chances of breaching.
Phishing
This generally happens with user when they click some malicious link tha appears and then they are caught hard by the attackers.
Pre texting and Social engineering
This might have happened with all. You get some message about some offer that is really irresistible but when you follow it they will ask for handsome amount of money for exchange of data.
Insider threats
The biggest threat to data security to an organization can come from within, where the intruders are from insider. But this one is preventable.
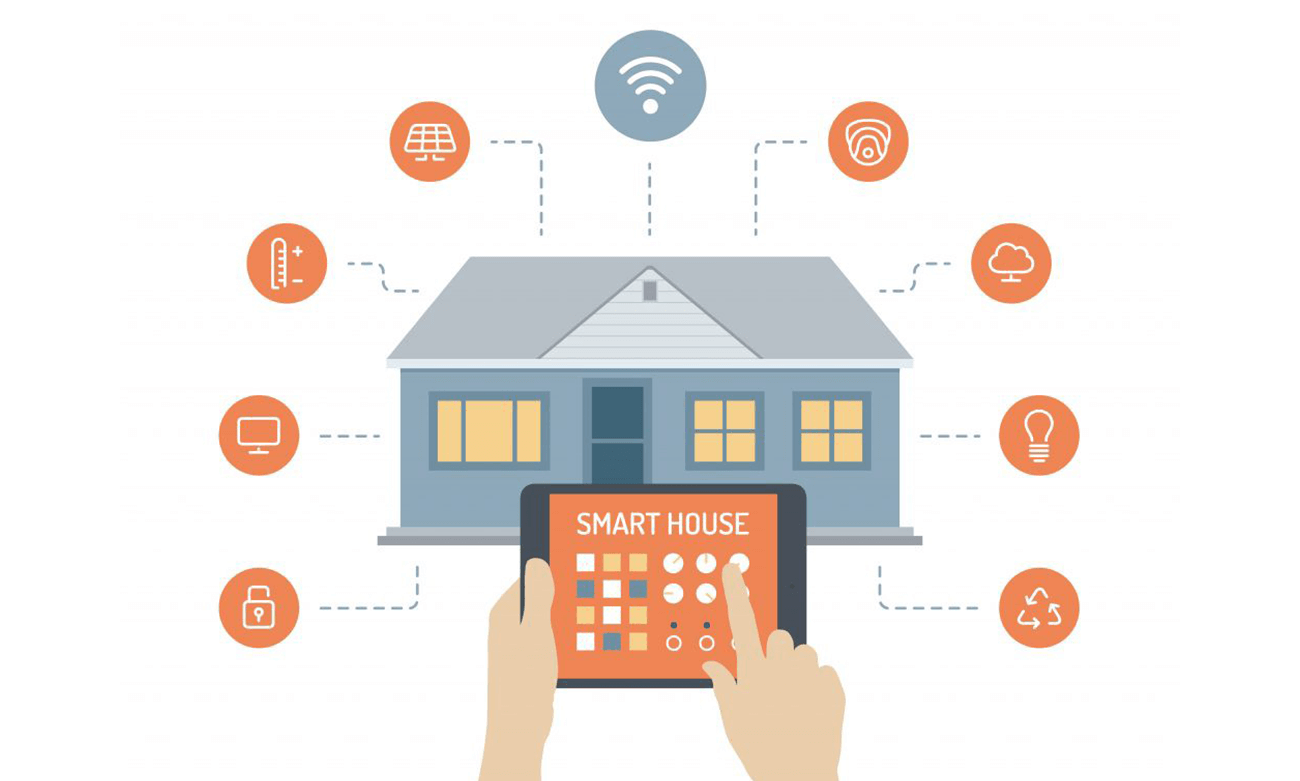
Application Vulnerabilities
Using software that is not updated or patched or applications that are poorly coded and may contain black holes often leave businesses open to data breaches and vulnerabilities. This can be fixed by implementing basic security hygiene by the IT departments of businesses.
Ransom ware
Vigilance is the best defense against ransom ware.
Physical theft and loss
Sometimes, they may also occur out of physical theft and loss. The cause for this may be unsecured ways in which physical storage devices are used.




Leave a comment: